Govt Abstract
Cisco has lengthy supplied safety providers for third get together occasions such because the Black Hat and RSA Conferences, in addition to the Tremendous Bowl and the Olympic video games. These providers come within the type of merchandise (Cisco Safety Cloud capabilities, together with Umbrella, XDR, Malware Analytics, and many others. plus Splunk Enterprise Safety); and expert Safety Operations Centre (SOC) analysts, who construct and function the infrastructure and hunt for threats, from each inside and outdoors the occasion networks.
For the second time at Cisco Stay APJC, the crew was tapped to help the Cisco Stay Melbourne 2024 convention. This report serves as a abstract of the design, deployment, and operation of the community, in addition to among the extra fascinating findings from 4 days of menace searching on the community.
SOC Evaluate
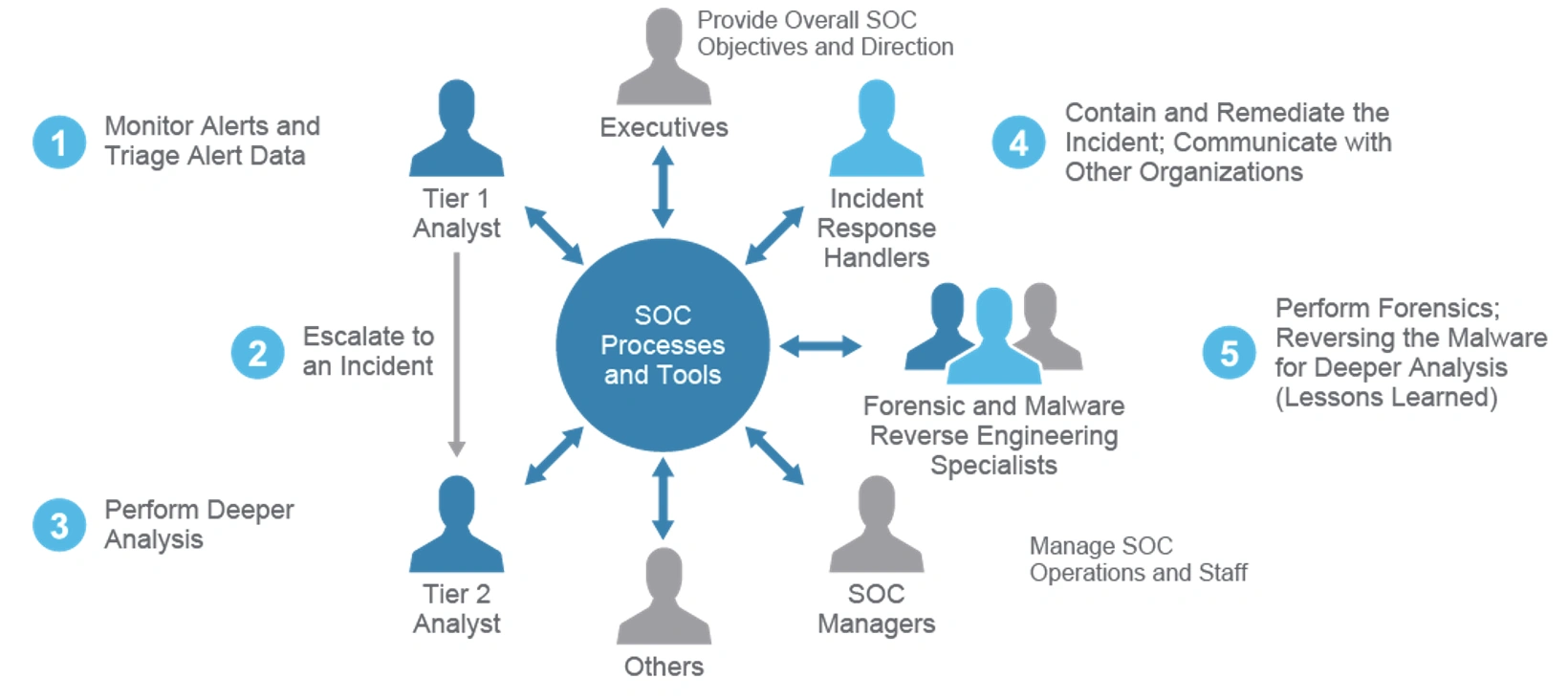
The Cisco Stay Safety Operations Centre (SOC) has a mandate to make sure entry to occasion providers is delivered securely. Reaching this objective requires monitoring and interacting with a number of merchandise to get the information wanted.
Receiving knowledge in lots of kinds from the community and gadgets permits the SOC to curate that knowledge to have the ability to higher discern what is definitely occurring within the atmosphere. We’d like summarized info to provoke triage, however the capacity to forensically examine in sure circumstances.
To higher perceive the dimensions of the operation that’s Cisco dwell APJC, take a look on the following statistics for the 4 Days of the convention
DNS Whole Queries: 48,123,933
DNS Queries Sinkholed: 4,750
Categorized Functions: 11,614
Dangerous purposes: 300+
Inside complete visitors: 320TB
Encrypted Visitors: 206TB
Visitors to Exterior: 314TB
Inside Distinctive Hosts: 4355
Exterior Distinctive Hosts: 58349
Enterprise Threat Areas
Cisco Stay occasion Surroundings:
- Occasion Wi-Fi – Delegate entry, Workers entry
- Cisco TV – Vital broadcast providers
- NOC/SOC operations – Vital Administration Companies
- World of Options – Demonstration Zone
- Registration – Occasion entry administration and safety passes
Preparation
“The Proper Device for the Proper Job”
Bumping into the atmosphere occurred the week earlier than the occasion however required months of preplanning. This included the logistics of staffing, flooring format, cloud Service builds, gear transport, advertising and marketing liaising and tour registration, escalation course of with the NOC Workers, and incorporating classes realized from earlier occasions. To not point out shift rosters and occasion passes.
Staffing


We proved a fourteen hour protection in 2 shifts, with “eyes on display screen” from 8 am till 6pm.
There have been at the least 4 stations chaired every with major focus of TRIAGE, SANDBOX, EVENTING, and SIEM/Forensics.
All workers rotated by these chairs, with ancillary workers performing menace searching duties and creating automations.
Senior Analysts and Interns alike shared expertise and data like buying and selling playing cards. All of us realized from one another and the comfortable supportive atmosphere maintained itself. The atmosphere not solely served to guard the attendees but in addition permits us to “beat up on” the platforms and present them in use, accumulating suggestions to supply to the builders all of the whereas studying and honing our analyst abilities.

Senior Analysts
Christian Clasen, Justin Murphy, Aditya Raghavan, Adam Kilgore, Tony Iacobelli, Jessica Oppenheimer
Intern Analysts
Cam Dunn, Milin Mistry, Ricky Mok, Zoltan Karczag, Alex Chan
SOC Leads
Shaun Coulter, Aditya Sankar, Ryan MacLennan
NOC Leads
Freddy Bello, Andy Phillips
SOC TOURS
Throughout the occasion we supplied fourteen SOC excursions which have been attended by a complete of 140 folks. The tour speak was to outline the aim of the SOC at that occasion, how we function, and a few fascinating tales of what we had discovered.
The SOC workers rotated by delivering these talks and fascinating finds by the convention.
The remainder of this weblog is a written model of these SOC tour talks, beginning with the construct and operation, the parts, and our analyst tales. Take pleasure in!
Construct and Operation
We function a triage tier to supply a abstract view using Cisco XDR and deeper forensics with Splunk Enterprise Safety. This method permits us to quickly perceive the chance and breadth of an incident, and mine the information deeply for circumstances with greater complexity.
With this method XDR successfully performs the duty of accumulating knowledge and placing it in context, in addition to present the suitable playbook to take care of the incident because it stands. Within the Cisco Stay SOC this quickens with work of Tier 1 triage.
SOC Structure
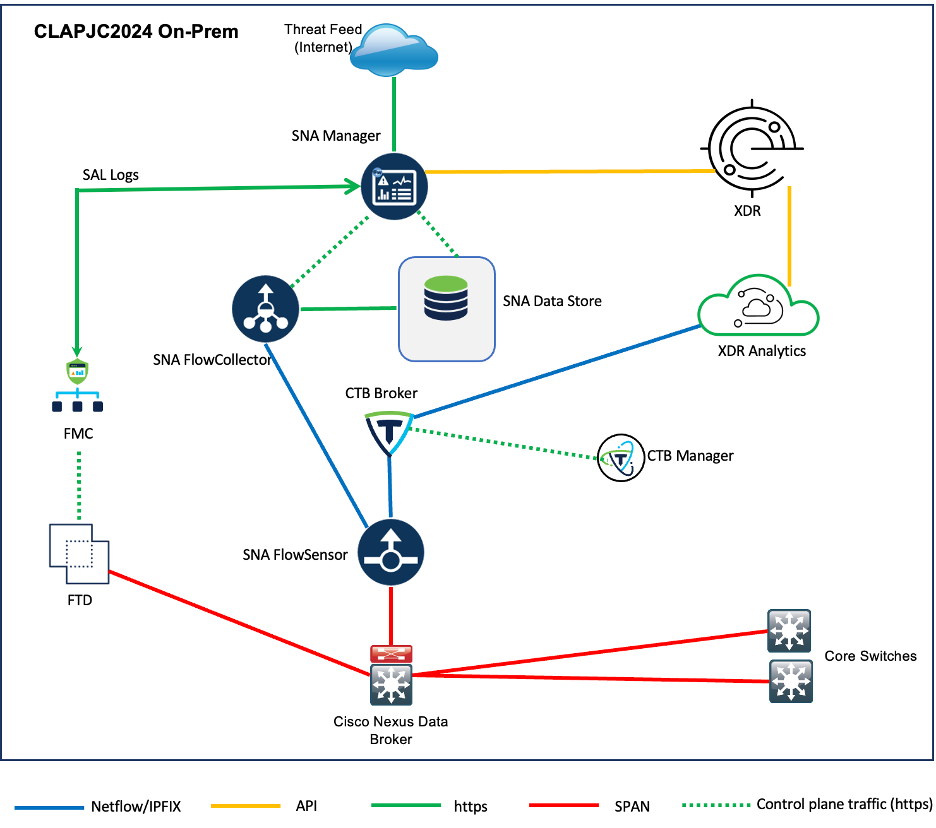
Cisco XDR and Splunk ES are built-in collectively and obtain related knowledge from all convention infra. Particularly, the next merchandise have been deployed to supply related knowledge:
On premise:
(Be aware the above platforms can be found individually or packaged in Cisco Safety Suites, confer with the next hyperlinks for extra particulars
The diagram beneath illustrates how the merchandise are logically interconnected.
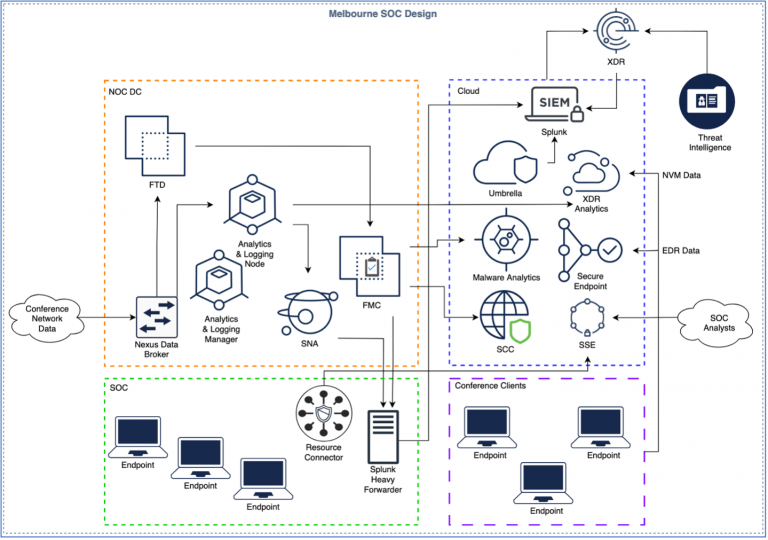
Trying on the picture above we see the convention community knowledge coming into the Community Operations Heart’s knowledge middle (DC) on the left aspect. The SOC is being fed the convention knowledge through a Nexus Knowledge Dealer.
To the appropriate of the NOC DC, we’ve our cloud-based merchandise. Below the NOC DC there’s a inexperienced field with the SOC analysts in it. This isn’t solely the place we sit but in addition the place we connect with our inner assets utilizing Safe Entry. We used the Safe Entry Useful resource Connector to hook up with inner assets just like the Firewall Administration Heart (FMC) and Safe Community Analytics (SNA). That is additional explored within the subsequent part of the weblog.
On the underside proper, we’ve Safe Shopper deployed on Home windows machines across the convention to ship NVM and EDR knowledge to XDR and Safe Endpoint. Lastly, we’ve all of the merchandise within the orange dotted field sending knowledge to XDR together with third-party menace intelligence feeds.
Inside the NOC DC space, we’ve the Nexus Knowledge Dealer SPAN, offering that feed to a bodily Safe Firewall Risk Protection (FTD) equipment. The FTD is managed utilizing a digital Firewall Administration Heart (FMC) and isn’t configured to implement any safety coverage. Beneath is an outline of what was configured:
- Community Evaluation Coverage
- Safety Over Connectivity IPS coverage
- File coverage together with AMP File Repute
- Logging in the beginning and finish of connections
- Integration with
- Umbrella for DNS
- Safe Malware Analytics for newly seen information and URLs
- Safety Analytics and Logging (SAL) integration for forwarding occasions to SNA and subsequently to XDR and to Splunk ES.
Following is a deeper take a look at every part.
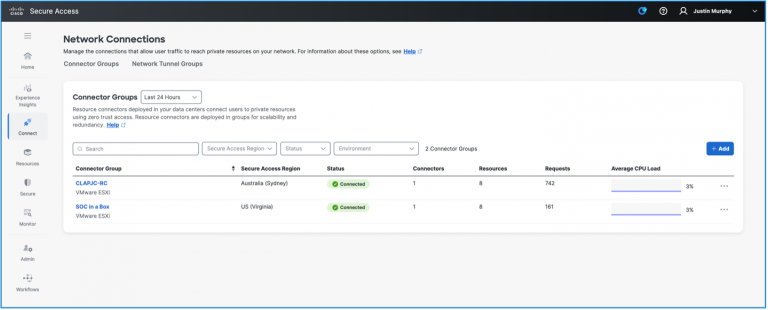
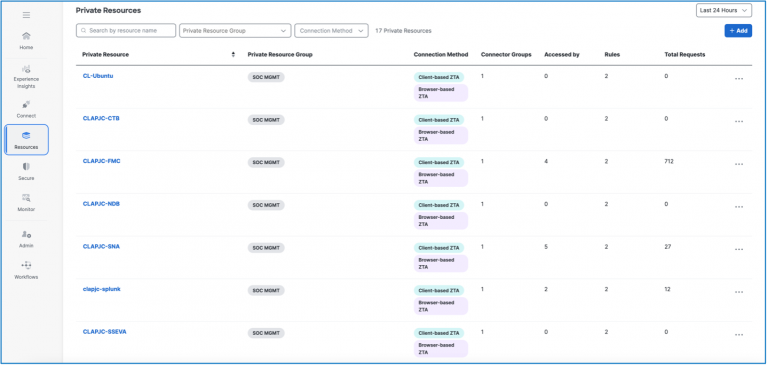
Cisco Safe Entry
Justin Murphy
Cisco Safe Entry (CSA) is Cisco’s Safe Companies Edge platform. Within the SOC we have an interest primarily in its functionality to supply entry to purposes from wherever to wherever.
To that Finish, Cisco Safe Entry was configured to supply entry to the on-premises platforms. Specifically: the Splunk forwarders, the SNA, the FTD, and the Telemetry Brokers.
The photographs present the configured assets that have been accessed with CSA, with redundant connector teams or head ends, and the statistics of the accesses to every of the assets.
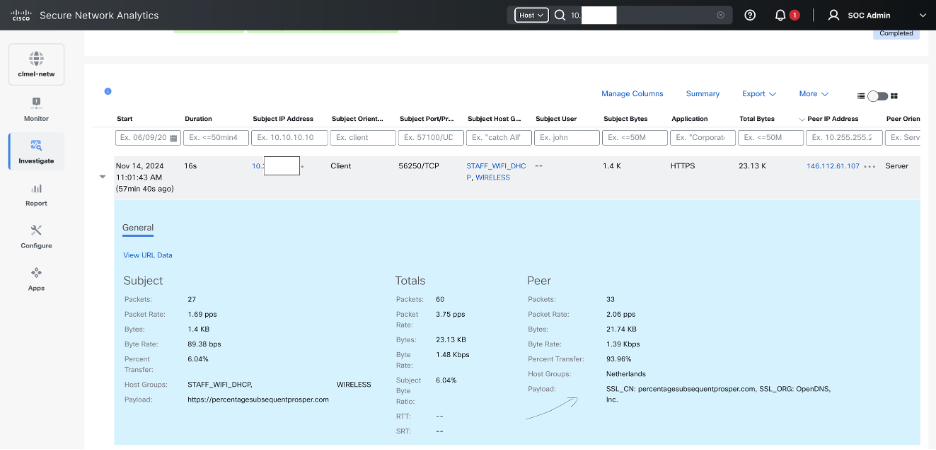
Cisco Safe Community Analytics
Cisco Safe Community Analytics (previously often called Stealthwatch Enterprise) supplies full visibility throughout the Convention community and makes use of superior analytics to detect and reply to threats in real-time. These threats embrace command-and-control (C&C) assaults, distributed denial-of-service (DDoS) assaults, unknown malware, and insider threats.
Safe Community Analytics is built-in with Cisco XDR, Vital and Main safety alarms are despatched from the Safety Companies Change and analyzed by the present platform to help investigations. These alarms are transformed into incidents, full with particulars like sightings, observables, and indicators primarily based on the alarm metadata.
Throughout an investigation, for each legitimate IP deal with requested, Safe Community Analytics supplies:
- A listing of related safety occasions from the final 30 days,
- The newest 100 safety occasions, and
- Occasions the place the IP was concerned as both the supply or vacation spot.
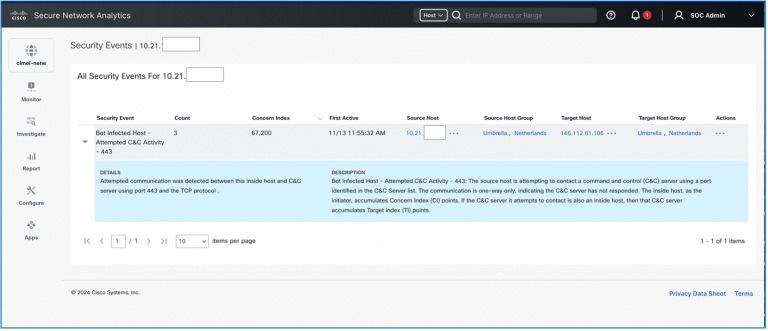
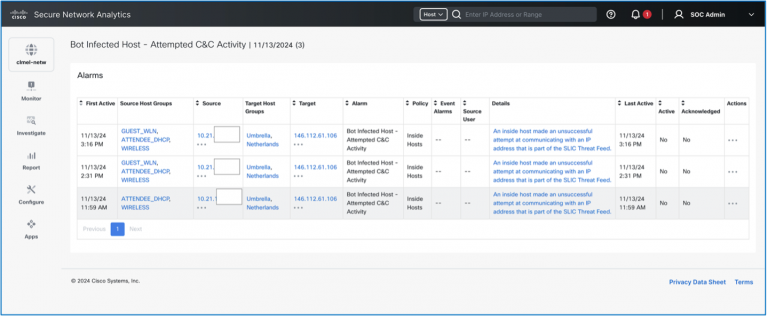
Along with commonplace fields contained in NetFlow/IPFIX data, the Safe community analytics FlowSensor additionally incorporates extra metadata from deep packet Inspection (DPI) for correct layer-7 utility identification, community, and server response time metrics, in addition to restricted packet payload info (together with as much as 256 bytes of HTTP and HTTPS request paths), which is used as required for forensic investigation.
Cisco XDR
Cisco XDR is a cloud-based answer designed to simplify safety operations and empower safety groups to detect, prioritize, and reply to classy threats. Within the Cisco Stay SOC, XDR is used because the triage platform. XDR receives telemetry from all integrations, and performs an occasion aggregation and correlation, to supply an incident bundle. It is a totally different method to a SIEM in that the search, danger evaluation and collation of sufficient knowledge to find out danger is an out-of-the-box operation. One may say it’s extra of a plug-and-play method. Customization is obtainable however to not the extent that our Splunk platform permits. We use XDR for Triage and Splunk ES for escalation. This works exceedingly effectively, and we’re capable of quickly upskill interns to be operational, whereas permitting senior analysts to focus on course of and automation enchancment and escalations. That is “the appropriate instrument for the job” at work.
For the Cisco Stay APJC 2024 SOC, a customized dashboard within the Management Heart was constructed to focus on the findings from the varied built-in options.
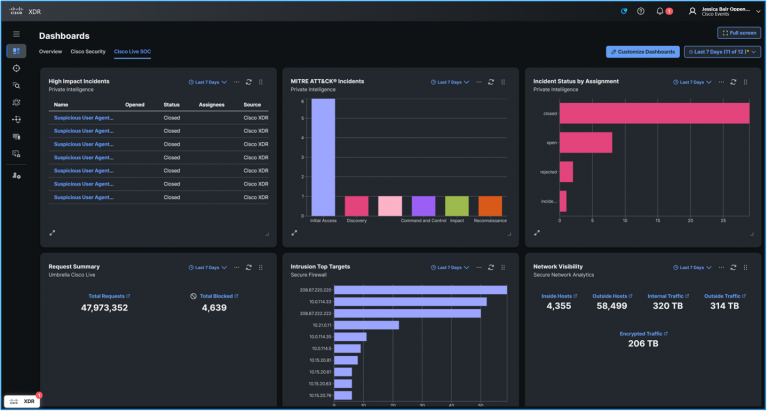
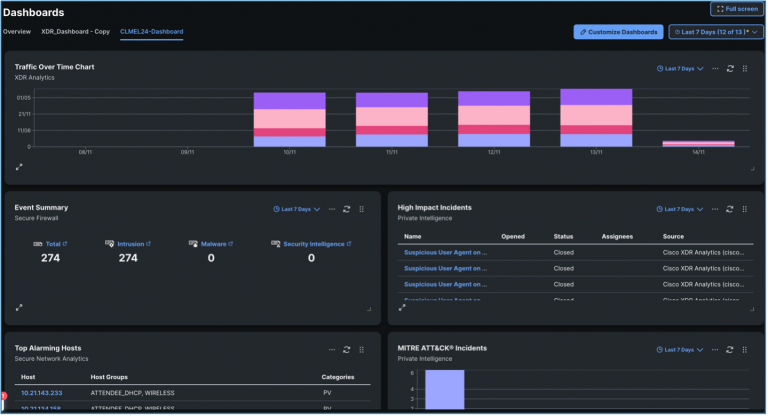
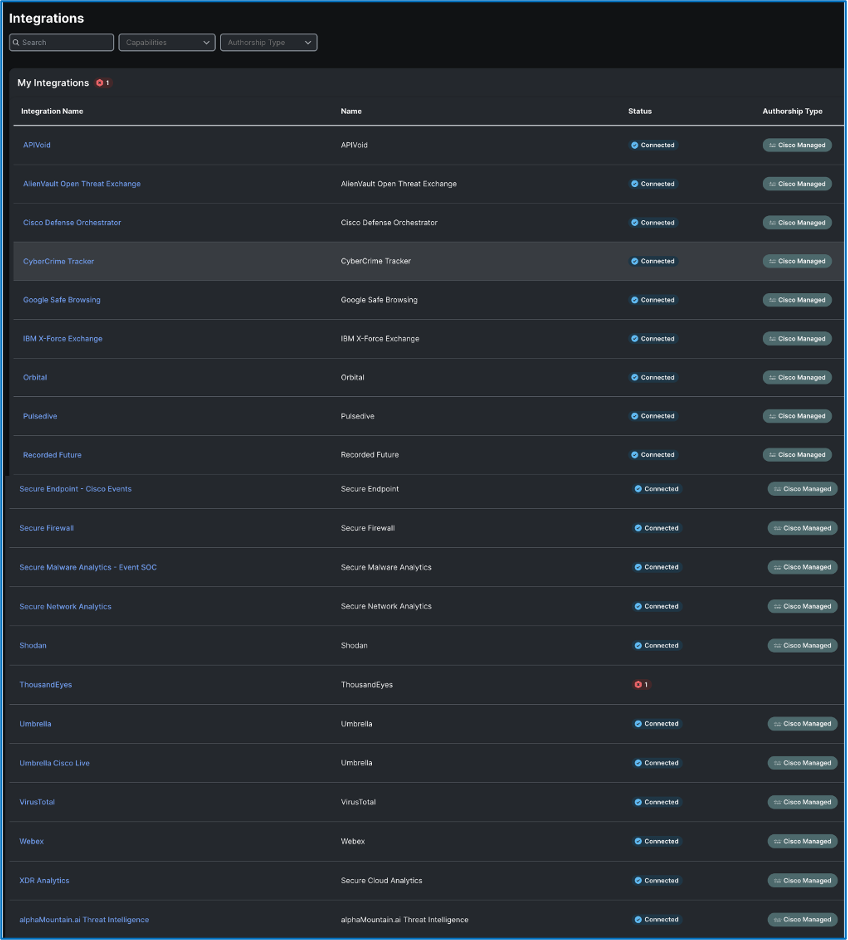
Following are the plug and play integrations which have been configured in XDR:
Splunk
Our Splunk stack consisted of Splunk Cloud and Splunk Assault Analyzer. Splunk Cloud had Splunk Enterprise Safety (ES) and the Cisco Safety Cloud apps put in. Since our safety instruments embrace on-premises home equipment just like the Firewall Administration Heart and the Safe Community Analytics Supervisor we would have liked to have the ability to get the information from on-premises to the cloud. The answer was to face up a UCS M3 server that we had on website. As soon as we obtained the server on-line, we deployed a small Ubuntu digital machine and put in Splunk on it.
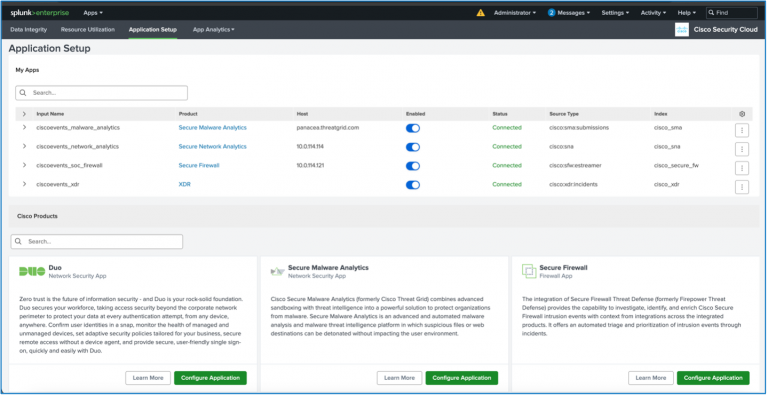
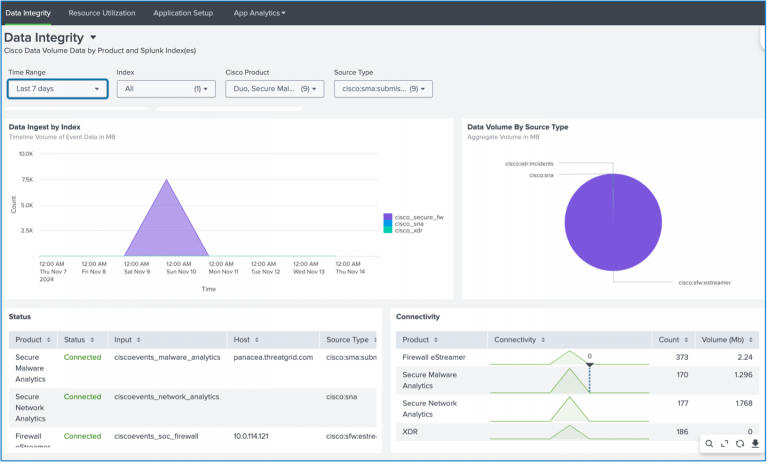
The Cisco Safety Cloud app, which is revealed on the Splunk base app retailer, is a single app to get knowledge from Cisco Safety instruments into Splunk. The app is modular so particular person merchandise will be configured to ingest knowledge into Splunk together with Safe Malware Analytics, Firewall, Safe Community Analytics, Cisco XDR and extra. The app features a pre-configured dashboard for every product and well being monitoring of the app to see how a lot knowledge is being ingested. When knowledge is ingested, the app transforms the information to a Widespread Info Mannequin (CIM) which is Splunk’s common schema for indexing knowledge. This enables us to create visualizations throughout a number of knowledge units or seek for a single subject throughout a number of telemetry sorts.
With the Cisco Safety Cloud app configured to ingest knowledge from our varied sources we then put in the common forwarder app to hook up with the Splunk cloud deployment. The common forwarder was extraordinarily performant and was capable of ahead gigs and gigs of knowledge to Splunk cloud with out ever exceeding 30% CPU or an inexpensive ingest delay. This allowed us as SOC analysts to look knowledge in Splunk cloud which can be the place we had Enterprise Safety put in. Incidents from XDR have been robotically populated as notables in Splunk ES.
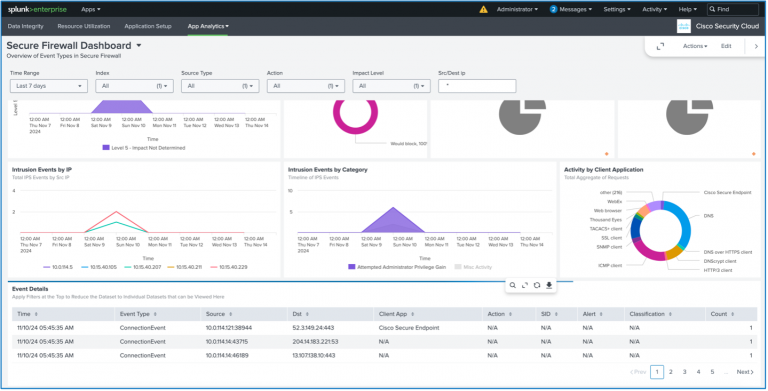
Safe Firewall Risk Protection
The Cisco Safe Firewall (CSF) deployment at Cisco Stay Melbourne is an IDS deployment that receives a TAP from the prevailing community and safety infrastructure utilized by the convention. CSF acts because the visitors ingestion level for the opposite safety instruments utilized by our SOC, accumulating helpful knowledge and producing logs and occasions which might be used to tell merchandise like Cisco Splunk and Cisco XDR. CSF additionally pulled information instantly from unencrypted classes, submitting them to Safe Malware Analytics for sandbox evaluation.
Working in passive IDS mode does have visibility drawbacks, as we lose the power to make use of TLS Server Id to drag extra info from HTTPS connections, and basic decryption is off the desk. Nevertheless, the firewall nonetheless supplies core alerting capabilities, and the handfuls of datapoints captured for every connection proved key in lots of investigations, most notably coated within the ‘Sifting Visitors with Safe Firewall’ and ‘Malware Callouts from the Present Flooring’ sections.
From a geolocation perspective, Cisco Stay attendees confirmed a powerful prevalence for connections again to the USA, dwarfing all different connection locations.
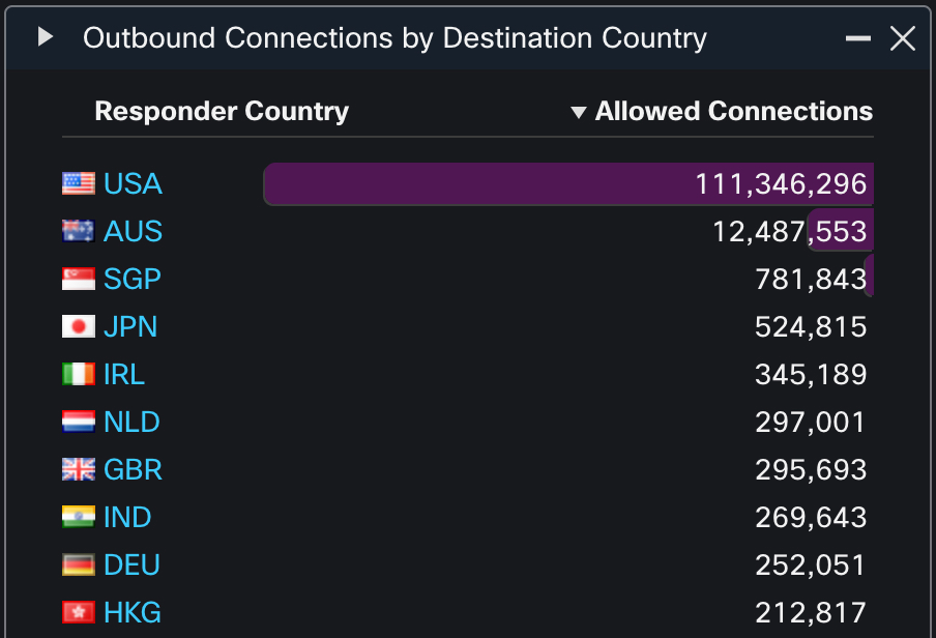
The house nation of Australia additionally made a powerful exhibiting with twelve million connections. No different nation cleared one million connections, however the remainder of the listing confirmed an unsurprising prevalence for regional and world tech hotspots. The predictability of geolocation preferences for the attendees allowed us to take a more in-depth take a look at rarer inbound and outbound geolocation connections, which helped us broaden a number of investigations as we appeared for added exercise after discovering one occasion. After all, geolocation knowledge for malicious exercise will be faked utilizing Tor, VPN, or a compromised host in a foreign country, however visitors that blends in with anticipated geolocation patterns continues to be subjected to signature, heuristic, and sandbox evaluation. Geolocation stays one among many traits that may reveal assault patterns.
Software knowledge is one other space that we monitor at a broad degree, along with particular person alerts for malicious domains. We proceed to see plaintext assaults and plaintext info leaks at every convention, however the frequency of those has progressively decreased. At Cisco Stay Melbourne 2024, we noticed a 15:1 desire for HTTPS over HTTP. HTTP/3 additionally continues to develop in recognition.
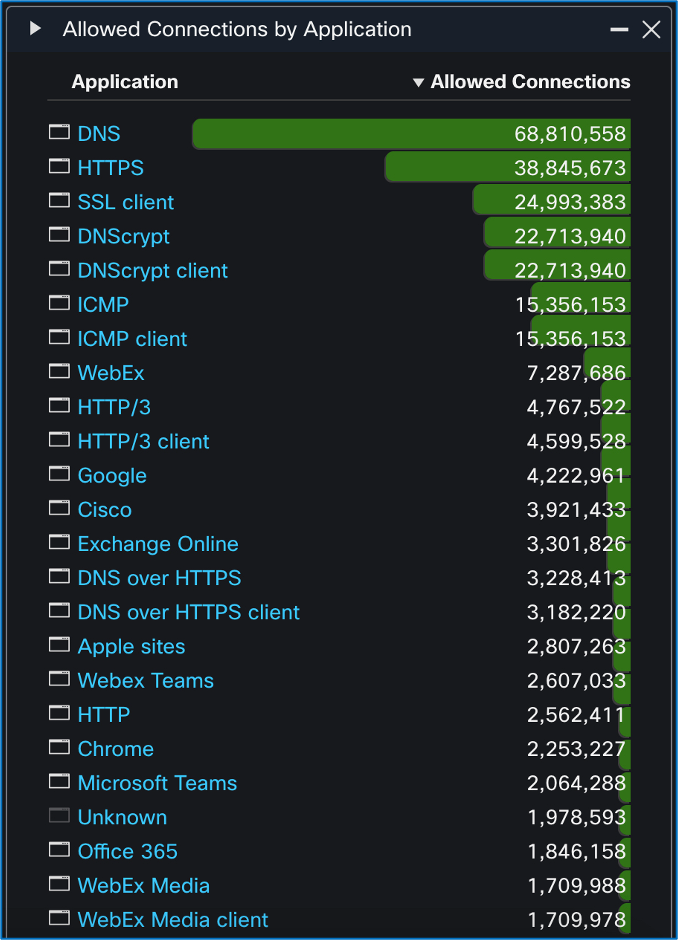
Additionally of word is the usage of DNS over HTTPS to masks DNS requests. Whereas the nice majority of DNS requests proceed to be plain textual content, the usage of DNS over HTTPS continues to rise. Ultimately, we count on to see plain textual content DNS requests overshadowed by encrypted DNS protocols, very similar to HTTP is eclipsed by HTTPS in the present day.
Automations
By Aditya Raghavan
On the automation entrance, we launched three new automation workflows to assist velocity up menace attempting to find our analysts. Credit score to Ivan Berlinson, our colleague from France, for the first two workflows in XDR automation with Safe Malware Analytics, and Adi Sankar for the workflow with Umbrella.
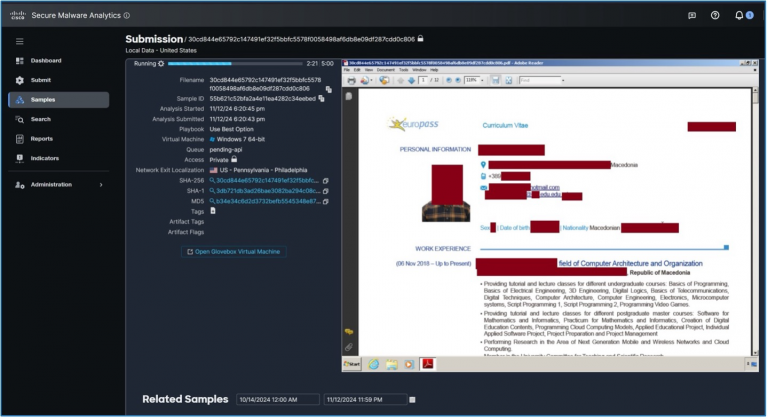
1. Malicious samples submitted in Safe Malware Analytics
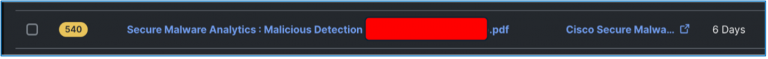
We wish to cut back the variety of dashboards pivots our analysts take care of. So, for any samples submitted to Safe Malware Analytics which might be convicted as malicious (menace rating > 90) and seen within the Cisco Stay atmosphere, this automation workflow would robotically create an incident in XDR and ship a Webex message to the Incidents channel. The above is an instance. Whereas this isn’t one thing to do in a manufacturing atmosphere each time, it’s helpful for effervescent up fascinating avenues of investigations proper in XDR and Webex to our analysts.
2. Non-malicious samples from frequent doc codecs
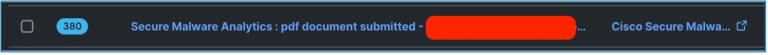
Equally, we sometimes see some content material transmitted in clear textual content at such occasions. Any paperwork with frequent file sorts submitted to Safe Malware Analytics having a non-malicious verdict (menace rating < 85), seen within the Cisco Stay atmosphere and of the next sorts sometimes have content material in clear textual content. That is value an investigation for our analysts to determine if there was any essential info being leaked inadvertently. This workflow would robotically create an incident in XDR and ship a Webex message to the Incidents channel for paperwork of the next file sorts.
- PDF, TXT, XLS, XLSX, XLSM, PPT, PPTX, PPTM, DOC, DOCX, DOCM
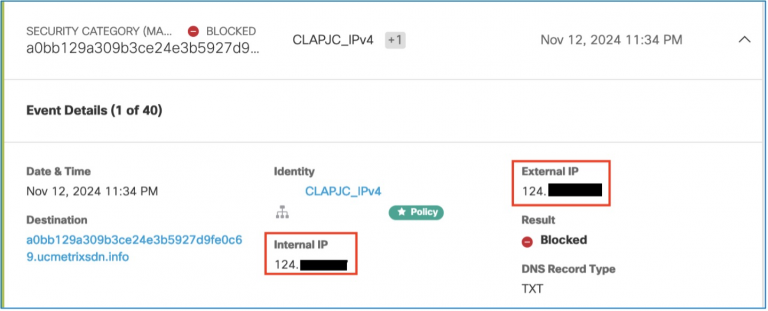
3. Create incidents from Umbrella Safety Occasions
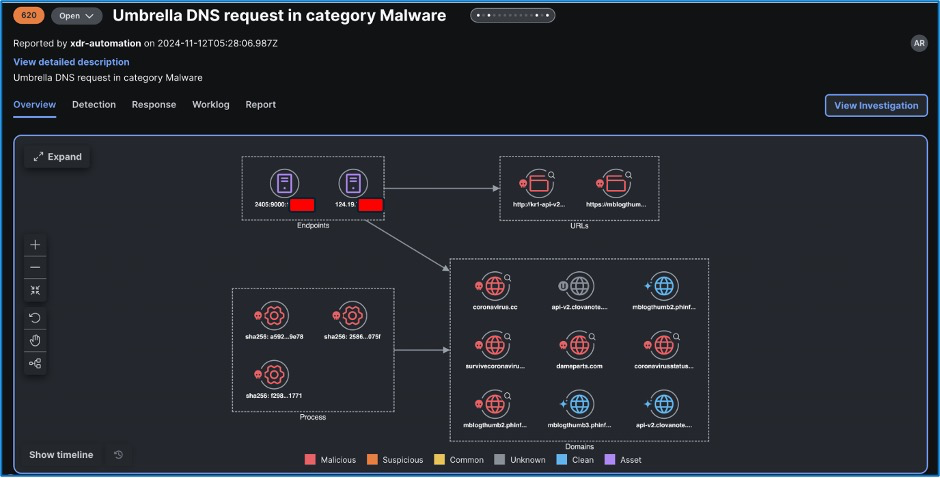
Any DNS Safety Occasions in Umbrella for sure classes of curiosity could be introduced ahead to the analyst as an incident per class. This reveals an instance of an automation created incident for the Malware class.
Analyst Tales
CoinLoader An infection Investigation
Christian Clasen
A pair days into the convention we seen a number of block occasions in Umbrella DNS. The occasions have been TXT file queries for what gave the impression to be randomly generated subdomains belonging to ucmetrixsdn[.]information. The queries resemble the area technology algorithm (DGA) approach generally deployed for malware beaconing.

DGA is a way in command and management (C&C) infrastructure that usually serves one among two functions: to retrieve directions from the malware’s authors or directors, or to exfiltrate knowledge from the contaminated endpoint by covert channels. As a result of this malware is well-known (first detected in 2018), we will use public intelligence to compile anticipated behaviors and extra indicators of compromise to start our investigation.
The DGA habits right here is well-known and attributed to the CoinLoader malware. Darkish Hint has an in depth write-up that supplied us some course: https://darktrace.com/weblog/catching-coinloader-decrypting-the-malware-hijacking-networks-for-cryptomining-operations. The questions we have been instantly seeking to reply have been:
- What was the present stage of the assault?
- Was there any danger to different attendees?
- Had the person been contaminated whereas on the convention community?
- Who was the person of the contaminated machine?
- Had been there different associated infections on the convention?
CoinLoader is an preliminary dropper designed to drag down different malicious payloads together with ransomware, info stealers, and cryptominers. It appeared that this specific an infection was seemingly at its preliminary stage, and Umbrella was efficiently stopping additional phases of an infection by blocking the C&C visitors. There was no visitors logged between this system and different attendee IP addresses, nor any scanning exercise so the chance to different attendees was presumed to be low.
The CoinLoader malware finds its victims by masquerading as cracked or pirated variations of reputable software program. To find out if the malware was downloaded on the convention community, we searched our SOC instruments (together with Safe Malware Analytics and Firewall file occasions) for cases of the file extensions RAR and ZIP, and any cases of filenames containing the strings “keygen” or “crack.” We discovered no proof that the malware was downloaded whereas on the convention community. As a result of we don’t decrypt attendee visitors, that is unattainable to know for positive.
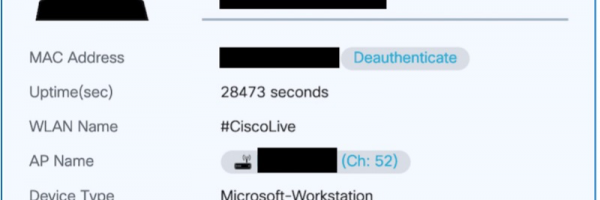
To seek out and notify the proprietor of the system, we used commonplace fingerprinting strategies. DHCP logs and visitors patterns are helpful for figuring out the OS and system sort. On this case, MDNS queries emanating from the system gave away each the working system sort and the hostname. The hostname contained the primary title of the attendee. Utilizing knowledge from the wi-fi infrastructure, we have been capable of bodily find the system on the present flooring.
With the person notified and the system triaged, we turned to additional searching of associated IOCs elsewhere on the community. We had a number of issues to search for together with:
- A particular string within the Issuer subject of the TLS certificates
- A particular ASN and publicly routable IP vary situated in Jap Europe.
- Addition C&C domains and URLs.
Utilizing Splunk, we have been capable of effectively search all our log sources for these IOCs and located no different cases of this an infection.
Methods for Shopper Attribution on Public Wi-Fi
Christian Clasen
Actual world deployments typically fall in need of the idealistic architectures supposed by distributors. Occasions, budgetary and time constraints, and technical feasibility typically conspire to forestall the maximalist method to safety infrastructure. When inevitably confronted with these challenges, analysts should depend on correlation strategies to benefit from the knowledge accessible within the SOC atmosphere. One such limitation we confronted within the Cisco Stay SOC was the dearth of Umbrella Digital Equipment (VA) integration resulting in a blind spot in our client-side IP visibility. With a bit of information of the mechanics of Umbrella operation, analysts have been capable of attribute malicious or suspicious DNS queries to shopper IP addresses on the general public Wi-Fi regardless of the dearth of VAs.
Umbrella is a recursive DNS resolver that makes use of the facility of the worldwide DNS to implement safety and acceptable use exercise. The general public IP addresses in use by the convention are registered to an Umbrella group in order that DNS queries will be attributed and dealt with by the appropriate insurance policies. Due to NAT, any IPv4 queries can be attributed to the general public deal with servicing all attendees. In an optimum Umbrella deployment, inner recursive resolver could be put in (VAs) and these would supply inner IPv4 attribution. Sadly, the inner resolvers used on the convention didn’t present this performance, and so Umbrella alerts solely supplied public IP deal with attribution.
The apparent answer to this is able to be to ingest the inner recursive resolver logs into our SIEM and SOAR infrastructure. This was deliberate and being actively labored on, however not instantly accessible within the earliest components of the convention. So the way to bridge this hole and make sure the most particular info is obtainable for these occasions? The reply is straightforward if you understand how Umbrella works.
When Umbrella determines {that a} question is for a malicious area, it doesn’t merely refuse the decision or return an NXDOMAIN response. It as a substitute resolves to devoted IP addresses owned by Cisco, after which waits for the next connection in order that it may possibly return a block web page. For HTTP/S connections, that is the easiest way to speak to the top person why their connection failed. Umbrella reserves particular IP addresses for area classes corresponding to Malware, Phishing, and Command and Management visitors: https://docs.umbrella.com/deployment-umbrella/docs/block-page-ip-addresses.
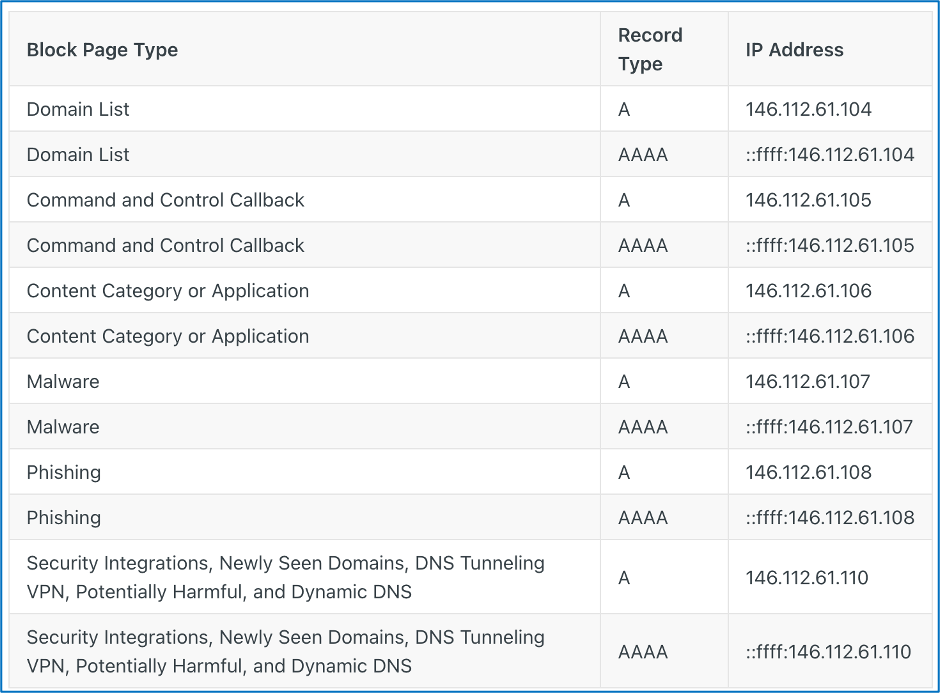
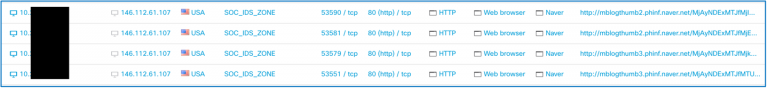
Armed with this info, there are two methods for correlating the Umbrella DNS occasions with Firewall occasions. By filtering the Firewall connections for the vacation spot IP deal with related to Umbrella Malware blocks (146.112.61[.]107) we will discover any connections the shopper subsequently made after resolving the malicious area. If the connection is tried over HTTP or HTTPS, we will very seemingly see the hostname within the HOST header or Server Identify Indication (SNI) extension subject. It is because the shopper nonetheless thinks it’s connecting to the supposed malware server, and never Umbrella.
For non-web visitors we will merely correlate the timestamp within the Umbrella occasion with the IP connection within the firewall occasions to find out with confidence that the particular inner shopper IP was the supply of the malicious or suspicious DNS question. From there, geolocation info from the wi-fi infrastructure may help us observe down gadgets and people when the content material of the alert warrants it.
Scraping Infra Servers
Aditya Raghavan, Adam Kilgore
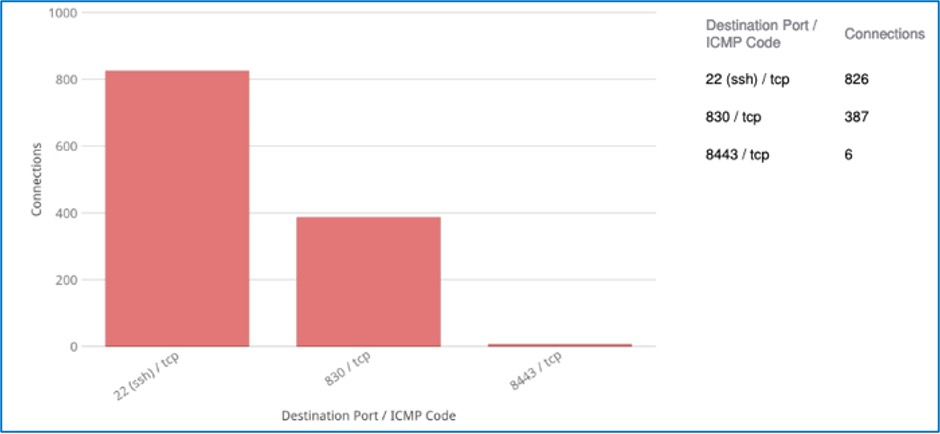
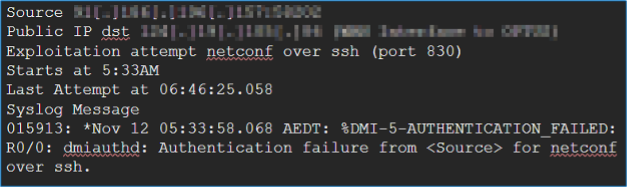
It began with Adam seeing a bunch of SSH connections from an IP within the DC static host group vary to some inner IPs on a non-standard port (TCP 830). Prima facie, all these connections have been profitable, so it appeared reputable.
We investigated the supply and vacation spot entities in XDR Examine and it discovered one other neighboring system from the Infra Administration host group additionally concerned in comparable visitors patterns. Moreover, the visitors between the gadgets in Infra Administration and DC Static host teams triggered a bunch of Snort signatures on the firewall.
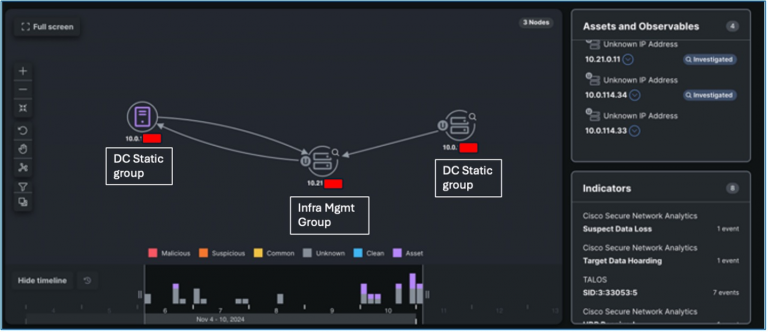
Safe Community Analytics validated the visitors patterns with Pretend Software Detected occasions. This was then escalated to the NOC crew because the Infra Administration section was beneath their possession.
Freddy Bello, the NOC lead, investigated it and recognized the entities as Wi-fi LAN controller (in Infra Administration) and DNA Areas Controllers (in DC Static). And the visitors sample involving SSH on a non-standard port was an app on the controller poking them to extract telemetry concerning the standing of the entry factors on the present flooring.
Whereas the visitors turned out to be anticipated, this can be a good instance of SOC workflows to research visitors patterns that seem irregular or may very well be an indication of compromise or malicious exercise if they aren’t confirmed to be from a reputable supply. By conserving an in depth working relationship with the NOC, we’re capable of present insights into visitors patterns and behaviors and obtain again affirmation of whether or not an investigation must be escalated or whether or not it may be safely closed. All in all, this turned out to be a Cisco Stay Constructive. On to seek out the following needle within the haystack, of us.
Suspect Knowledge Loss and Port Abuse Incident
Zoltan Karczag, Cam Dunn, Christian Clasen
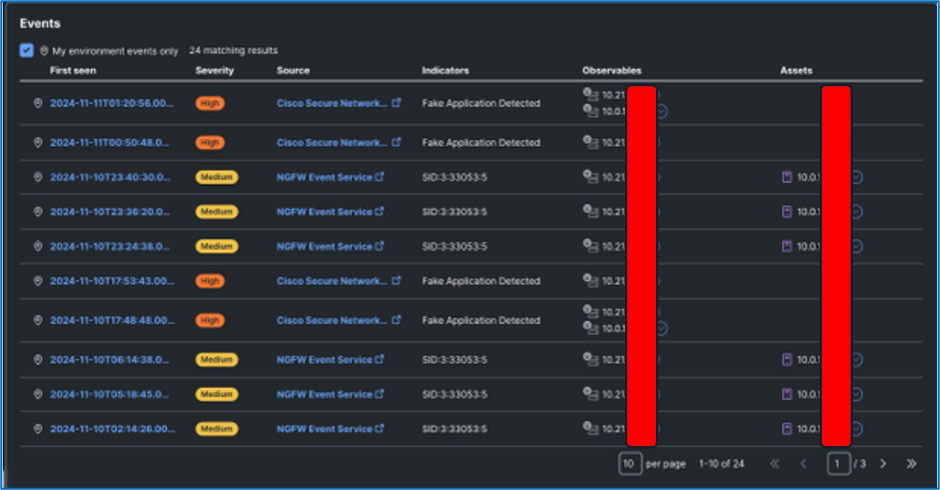
The SOC obtained notification from the NOC of some exercise that was seen by them on their WAN router:
This exercise was dropped by an ACL on the WAN router and by no means made it to the firewall, so was not seen by the SOC.
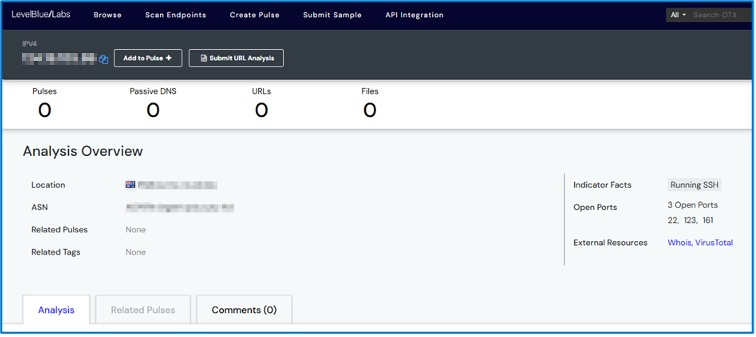
A reverse lookup of the IP deal with recognized that the visitors was as originating from Russia:
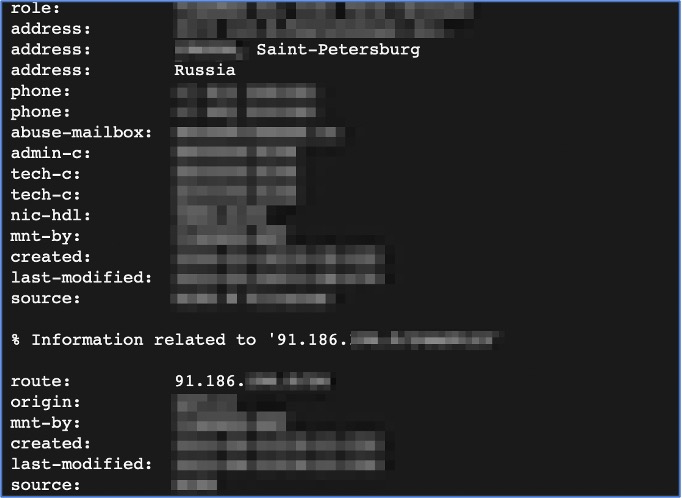
As a consequence of the above, the onsite NOC’s personal investigation into this resulted in an XDR incident seen on 12/11/2024, with the title as per the story title. See screenshot beneath:
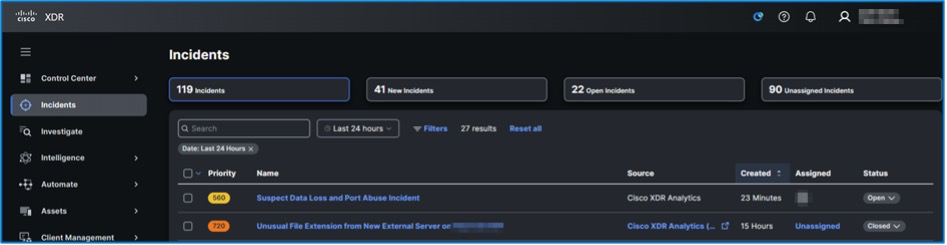

Investigation of the incident confirmed that the NOC initiated a port scan from an inner IP deal with to the WAN hyperlink.
One other Cisco Stay Constructive.
Suspicious Person Agent on
Christian Clasen, Zoltan Karczag, Cam Dunn, Ricky Mok
A number of incidents seen in XDR of suspicious person agent for varied IP addresses within the Cisco Stay occasion inner IP deal with vary.
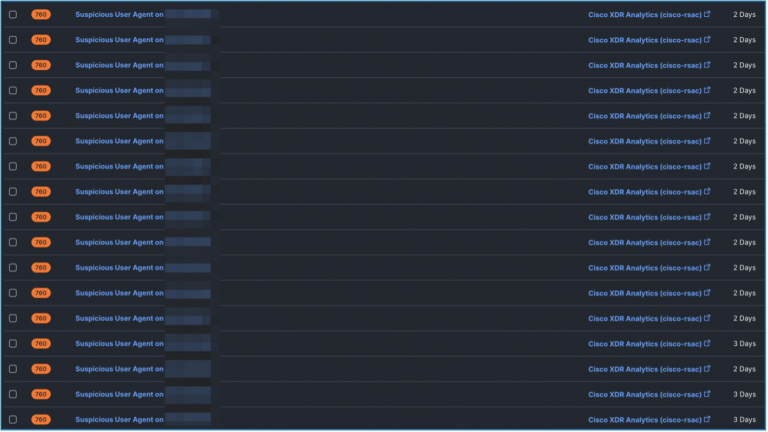
Investigation reveals that It’s resulting from an (seemingly Android) utility with a poor implementation of the OkHTTP shopper library (https://sq..github.io/okhttp/). The builders of the app aren’t correctly setting or calling the “challenge.model” variable of their app.
It’s more than likely to be one thing operating on this e-commerce platform https://open.lazada.com/
The server aspect implements Octopus https://octopus.com/docs/octopus-rest-api
Investigation through Safe Malware Analytics reveals the next:

Through XDR Examine:
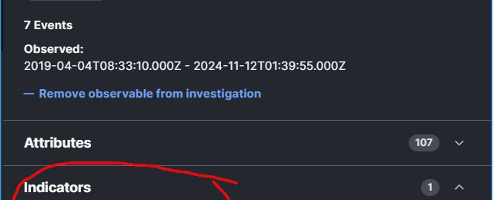
We lowered the precedence in Community Analytics on the suspicious person agent to cut back the variety of alerts in XDR for the legitimate benign person brokers detected.
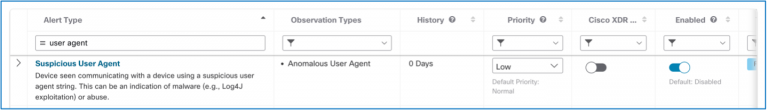
Additional refinement may very well be accomplished by blocking/filtering the particular noticed person agent.
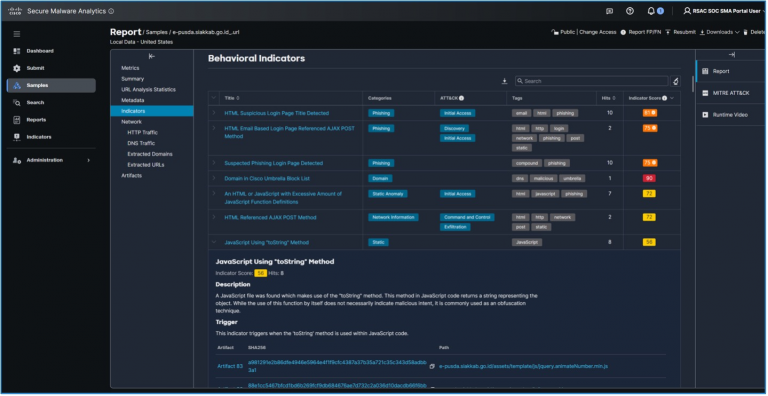
Suspected Phishing Area
Adam Kilgore, Zoltan Karczag, Tony Iacobelli
- Cisco XDR Alerted on a potential phishing area that was noticed by a bunch on the community
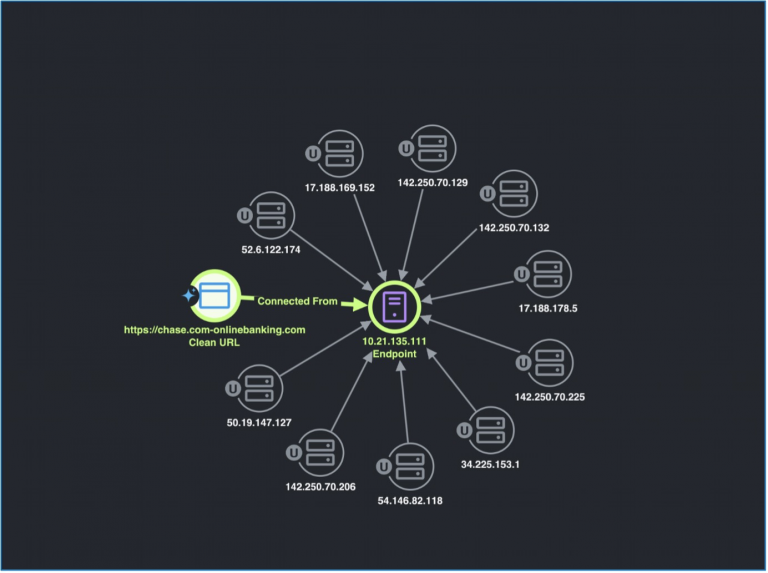
The SOC used Splunk Assault Analyzer to work together and analyze the web site in a protected approach, evaluation returned a “404 web page not discovered” website when the URL was triaged.
By means of additional investigation we have been capable of validate that the top-level area and related public IP have been owned by “knowbe4” which is a safety firm specializing in phishing simulation and coaching.
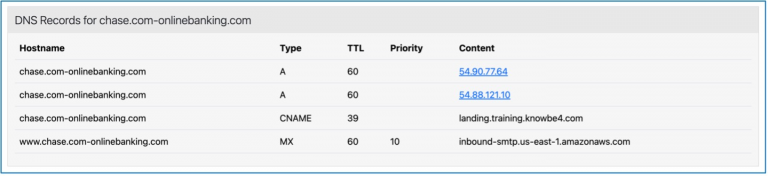
In accordance with this we recognized potential Cisco Stay attendees that had simply failed their group’s phishing evaluation.
Sifting Visitors with Safe Firewall
Adam Kilgore
Plenty of trendy analytics work is pushed by automation, and rightly so—the Melbourne SOC benefited enormously from the superior correlation supplied by the Cisco Splunk and Cisco XDR platforms. The large quantity of knowledge noticed and picked up by Cisco Safe Firewall is instrumental in feeding these superior analytics platforms. As well as, the information can be helpful in its personal proper, and I’m a private believer in checking datasets for the surprising.
We will test for surprising visitors by testing assumptions. One assumption we may make is that port 443 visitors can be HTTPS. Safe Firewall gives the logging, utility detection, and search granularity to confirm, utilizing a search just like the one beneath:

If the question returns nothing, then we proved our speculation—all of the 443 visitors in our logs is HTTPS. But when the question does return logs, then we’d have one thing value trying into, and on the very least one thing we’ll wish to perceive. For Melbourne Cisco Stay, our search did return some logs:
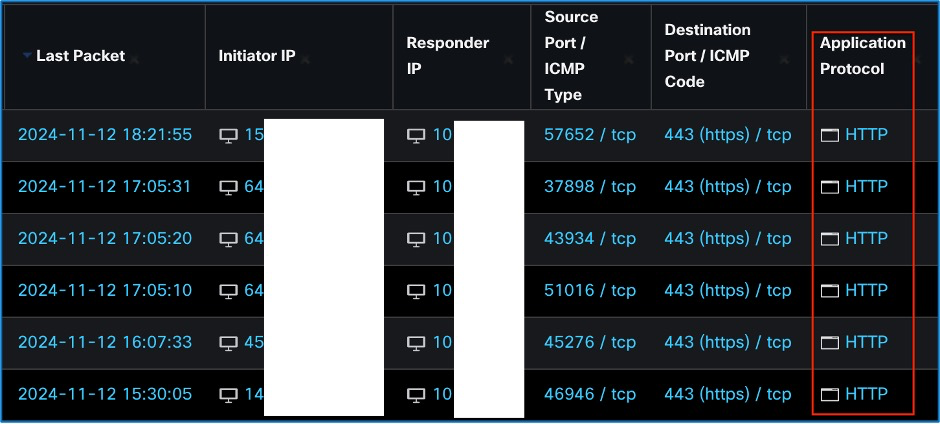
We will see from the above that we’ve some HTTP visitors operating over port 443. That’s not anticipated, so it’s value digging into it a bit of extra to see if we will work out why it’s occurring and whether or not there may be any safety concern. Because the visitors is HTTP protocol, we will test the URL subject within the logs.
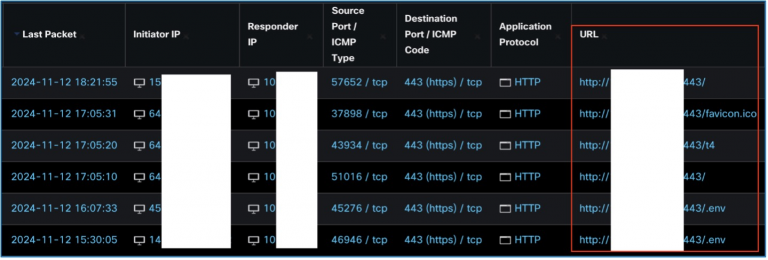
The URLs above specify a vacation spot IP and port 443, however some additionally append a path. Of specific word is “./env.” If improperly configured, the “./env” path on a server can reveal delicate info that would result in the compromise of the server and function an entry level in the direction of a extra severe assault. By narrowing down a big subset of anticipated visitors (HTTPS over port 443) we’ve remoted a a lot smaller subset of surprising visitors (HTTP over port 443) that additionally has a excessive focus of malicious exercise.
There are two issues we will do with this knowledge: (1) search for different malicious exercise from the identical actors, and (2) verify whether or not the “./env” requests efficiently retrieved delicate info from the servers. For (1), a straightforward methodology is on the lookout for different exercise from the identical IP addresses, however that is restricted since an attacker can alter their IP deal with utilizing Tor, a VPN, or a compromised host that acts as a soar server from which to launch assaults. Nevertheless, even when the attacker varies their IP deal with, generally we will nonetheless tie an assault to a person actor by accumulating a singular or semi-unique identifier from a identified assault (like a person agent) after which checking for a similar identifier in visitors from different IPs. For (2), we will simply decide whether or not the assault was profitable by trying on the packets within the server response, however these received’t be accessible until we have been operating a packet seize when the assault transpired, or if we’ve a knowledge lake that captured the connection.
If we don’t have the luxurious of a packet seize, we should be capable to decide whether or not the assault was profitable utilizing the firewall logs. If we broaden our firewall log search to incorporate the packets and bytes columns, we will decide much more concerning the assault and what knowledge was returned.
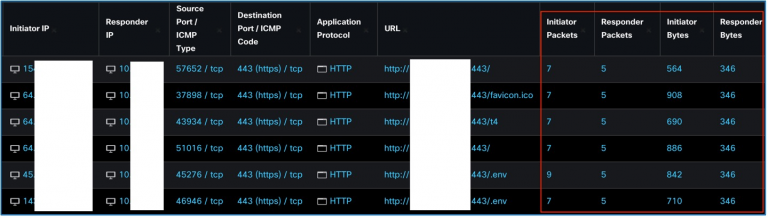
Utilizing the packet fields, we will see that a lot of the connections have seven Initiator Packets. For HTTP, the packets from the initiator IP can be a SYN for the primary packet, a SYN/ACK for the second packet, after which a GET request within the third packet. This third packet is the URL we see within the logs above, attempting to retrieve the “./env” knowledge in among the requests. Equally, within the Responder Packets column, we will count on an ACK for the primary packet, after which a response to the GET request that returns some type of info within the second packet. Our concern is that the knowledge returned for the “./env” requests is totally different than the information returned from the non-malicious GET request to the server, and whether or not that response accommodates delicate info. Can we decide whether or not that is occurring simply primarily based on the logs? We will, by trying on the bytes. For all of the requests above, we see the response is 5 packets, and the Responder Bytes are at all times 346 bytes. This tells us that the server is returning the identical response to every of the requests, or one thing very shut, for every of the requests within the logs, a few of which are attempting to entry “./env” and a few which aren’t. If the server did return server knowledge for the “./env” request, we’d count on to see a variation within the Responder Bytes.
Unsecured Transmissions
Jessica Oppenheimer
At every occasion, it is not uncommon to look at paperwork containing enterprise data, monetary knowledge, or private figuring out info. When potential, we find the individuals affected by the inadvertent disclosure over the community and assist them safe their communications. Usually it’s an insecure electronic mail protocol or open community connection, corresponding to http over port 80 as a substitute of https.
A convention is a superb place for networking, securely. We noticed a CV was accessed and detonated in Safe Malware Analytics. Investigation discovered the server was not transmitting the information over an encrypted connection.
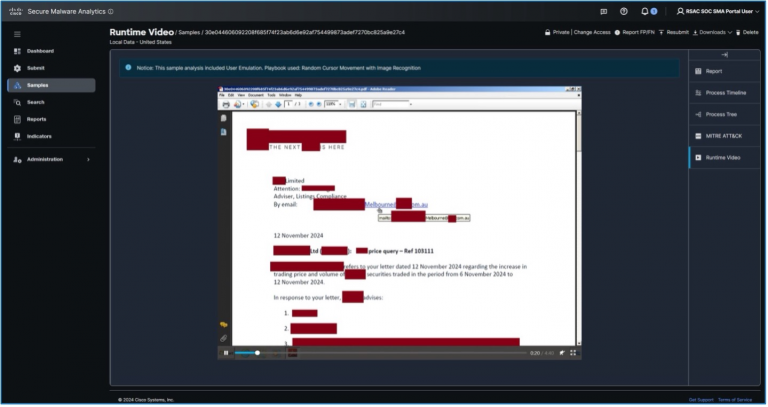
In one other case, enterprise data have been transmitted within the clear, once more from an internet connection over http.
Search for the safe connection icon in your browser and test your electronic mail settings to make sure POP3 or IMAP aren’t mistakenly chosen.
We additionally used the Glovebox function in Safe Malware Analytics to research web sites that convention delegates tried connection, corresponding to this seized area by legislation enforcement.
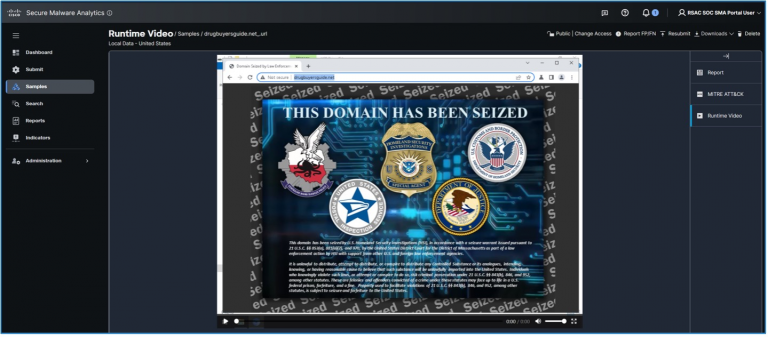
We have been capable of discover the habits of internet sites (corresponding to dropping malicious JavaScript information) with out our analysts changing into contaminated.
Additionally, the analysts can evaluation the Runtime Video to know the person expertise.
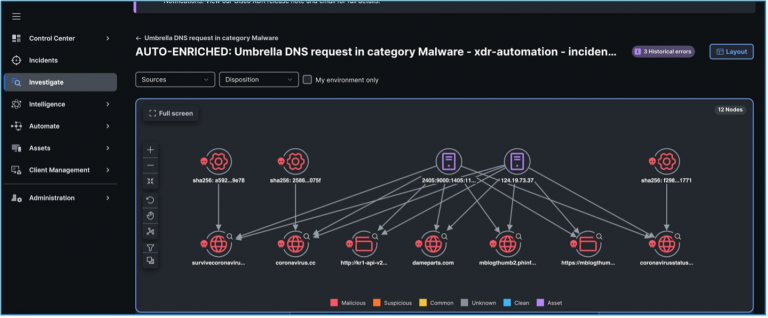
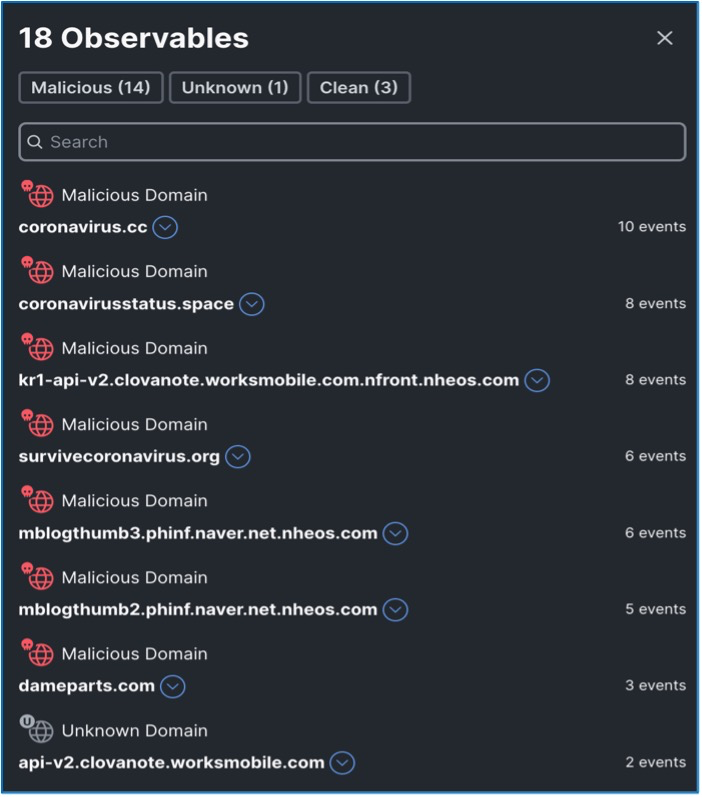
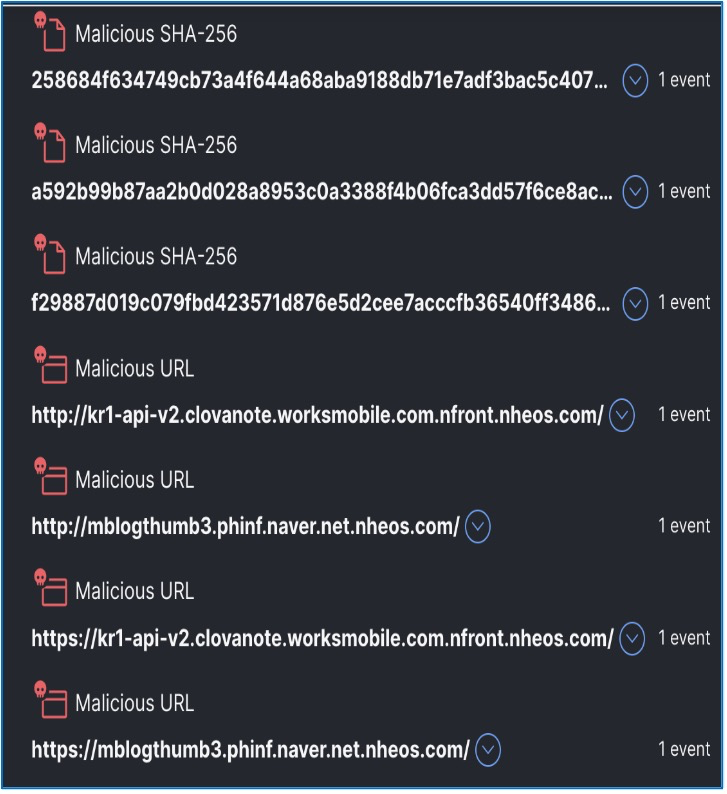
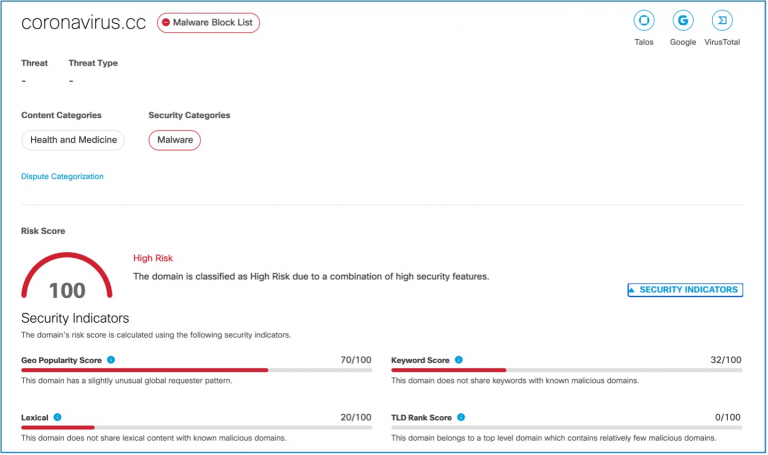
Umbrella DNS request in class Malware
Adam Kilgore, Zoltan Karczag, Ricky Mok
XDR automation through Umbrella connection Recognized variety of malicious domains related to by an inner host on the IPv6 community since Nov 11th, 2024. the noticed habits continues energetic on Nov 12th, 2024
Proof captures on XDR that listing the malicious domains and hash values.
Suspicious Callouts from the Present Flooring
Adam Kilgore and Christian Clasen
We picked up some DNS requests to a website beforehand related to an Iranian APT and a number of strains of malware.

A DNS request is only one IoC in an investigation. With a full enterprise deployment, we’d wish to observe down what utility made the request, when it was put in, and whether or not there was a reputable instance of person exercise that would clarify the DNS request and make sure it as not malware associated. Since we don’t have endpoint safety assets at our disposal for visitor wi-fi connections, and given the potential severity, we determined to see whether or not we may determine the top person system and notify them of the potential compromise.
Nevertheless, our lack of endpoint management makes identification troublesome as effectively. The visitor wi-fi connection is supplied totally free, with out requiring particular person login credentials or MFA. The place we may usually fall again on authentication logs from providers like Lively Listing and ISE, on the Melbourne SOC we needed to tie the IP again to an id going purely off community exercise. Is that potential? On this case, it was potential utilizing logs from Safe Firewall.
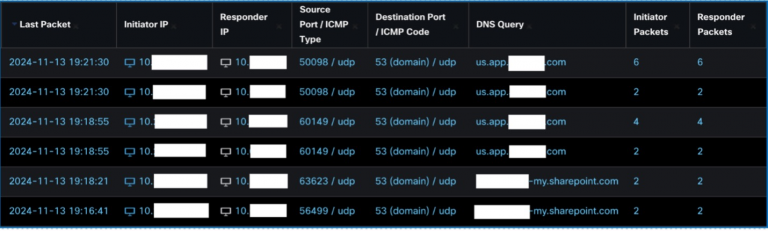
We put loads of belief within the safety of purposes and cloud providers. Whereas the encryption of those providers is normally effectively configured, they will nonetheless share fairly a little bit of figuring out info in those self same encrypted classes. Within the above instance, each a corporation app and a corporation SharePoint occasion revealed a selected vendor. And whereas we didn’t see it right here, different purposes like Slack may even reveal the room {that a} person is connecting to in an encrypted session. Is that an issue? Sure and no. The contents of the connections are encrypted and secured, however somebody with visitors sniffing capabilities (like we’ve through our TAP within the SOC) can nonetheless use that safe connection to tie visitors again to a corporation, a person, or an government function. A malicious actor may then goal the recognized group, group, or government through their now identified IP. Or in our case, we will use the datapoints of the potential malware callout, the corporate app, and the corporate SharePoint to inform somebody that their system may very well be compromised.
So, we now have an IP and a vendor title. Time to hit the present flooring. We discovered the sales space of the seller and requested them to substantiate whether or not one among their gadgets had the IP that made the DNS request—an ipconfig confirmed they did, which was not stunning given the connections made to the SharePoint and firm app. We notified them of the DNS requests that began the investigation and beneficial that they deal with the system and the related accounts as doubtlessly compromised.
Particular Thanks
Acknowledgments
Thanks to the Cisco/Splunk SOC crew:
Senior Analysts
Christian Clasen, Justin Murphy, Aditya Raghavan, Adam Kilgore, Tony Iacobelli, Jessica Oppenheimer
Intern Analysts
Cam Dunn, Milin Mistry, Ricky Mok, Zoltan Karczag, Alex Chan
SOC Leads
Shaun Coulter, Aditya Sankar, Ryan MacLennan
NOC Leads
Freddy Bello, Andy Phillips, Darren Nirens
Cisco Advertising
Vanessa Carlson!! Lauren Frederick, Trish Stallone
Additionally, to our SOC companions for licensing
| 3rd Celebration Integrations |
|---|
| APIVoid |
| AlienVault OTX |
| Cyber Crime Tracker |
| Google Protected Searching |
| IBM X-Pressure Change |
| Pulse Dive |
| Recorded Future |
| Shodan |
| Virus Whole |
| Alpha Mountain Risk Intelligence |
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share:
